Triggers
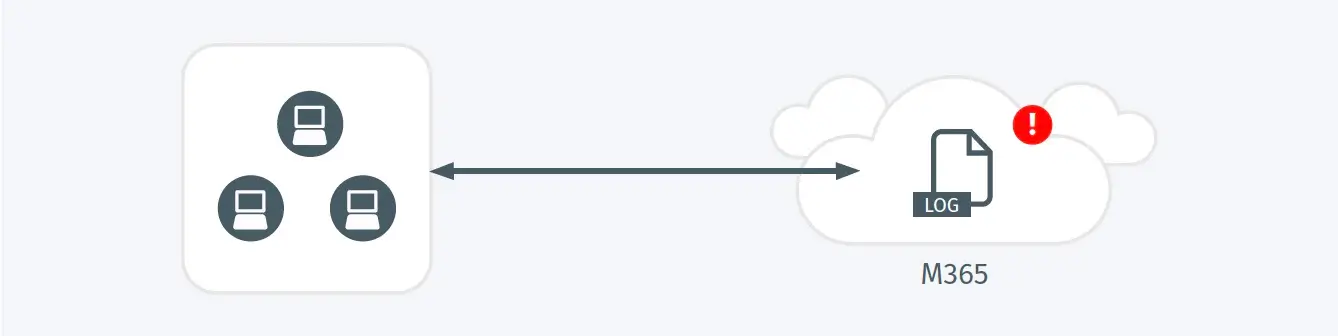
- An attempt has been made to disable important Office 365 logs that enhance security.
Possible Root Causes
- Attackers will seek to disable logging to blind detection mechanisms and cover their tracks.
- Logging may be temporarily turned off by an admin while changing configuration or troubleshooting a problem.
Business Impact
- An attacker who has disabled logging may progress parts of an attack without being detected, and without producing an auditable record to aid in forensics.
- Disabling logging degrades a critical component of an organization’s security architecture.
- Many audit and compliance requirements can only be met through the collection of activity logs.
Steps to Verify
- Review whether this logging configuration is expected and appropriate.
- If this is a temporary configuration for troubleshooting purposes, confirm it has been reenabled once that troubleshooting is complete.